...
- FLEXDEPLOY_HOME - Directory on the server where FlexDeploy is installed
- KEYSTORE_PASSWORD - The Java key store password.
- PRIVATE_KEY_PASSWORD -The private key password.
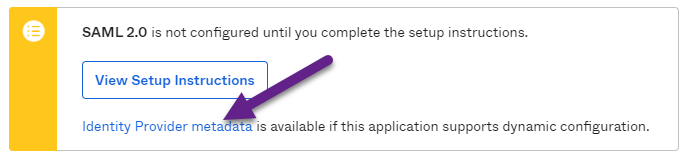
- OKTA_METADATA_URL - The URL (from Okta) to the identity provider metadata (e.g. https://dev-484624.okta.com/app/exk4c1ilhiTs3dKRb4y5/sso/saml/metadata).
- FLEXDEPLOY_HOST - FlexDeploy application host
- FLEXDEPLOY_PORT - FlexDeploy application port
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
saml2Config = org.pac4j.saml.config.SAML2Configuration saml2Config.keystorePath = FLEXDEPLOY_HOME/apache-tomcat-flexdeploy/certs/samlKeystore.jks saml2Config.keystorePassword = KEYSTORE_PASSWORD saml2Config.privateKeyPassword = PRIVATE_KEY_PASSWORD saml2Config.identityProviderMetadataPath = OKTA_METADATA_URL saml2Config.maximumAuthenticationLifetime = 3600 saml2Config.serviceProviderEntityId = https://FLEXDEPLOY_HOST:FLEXDEPLOY_PORT/flexdeploy/callback?client_name=SAML2Client saml2Config.serviceProviderMetadataPath = FLEXDEPLOY_HOME/apache-tomcat-flexdeploy/sso/FlexDeployMetadata.xml saml2Client = org.pac4j.saml.client.SAML2Client saml2Client.configuration = $saml2Config clients.callbackUrl = https://FLEXDEPLOY_HOST:FLEXDEPLOY_PORT/flexdeploy/callback clients.clients=$saml2Client isAuthenticatedAdmin = org.pac4j.core.authorization.authorizer.IsAuthenticatedAuthorizer excludedPathMatcher = org.pac4j.core.matching.matcher.PathMatcher excludedPathMatcher.excludedPath = /faces/login.jsf config.authorizers = admin:$isAuthenticatedAdmin config.matchers = excludedPath:$excludedPathMatcher ssoFilter = flexagon.fd.ui.security.FlexPac4jFilter ssoFilter.config = $config ssoFilter.clients = SAML2Client ssoFilter.matchers = nocache ssoFilter.authorizers = admin logout = io.buji.pac4j.filter.LogoutFilter logout.config = $config logout.localLogout = true logout.centralLogout = true logout.defaultUrl = https://FLEXDEPLOY_HOST:FLEXDEPLOY_PORT/flexdeploy |
| Tip | ||
|---|---|---|
| ||
If the Java keystore referenced (line 2) does not exist, it will automatically be created, and key will be generated and inserted into the keystore using the passwords provided (line 3 and 4). The Okta Identity Provider Metadata can be found from within the Sign-on tab of your Okta application. |
Azure Active Directory
...